Welcome to Googie Store India (Indian Digital Dukaan)

By continuing, you agree to Googie Store Terms of Use and Privacy Policy.
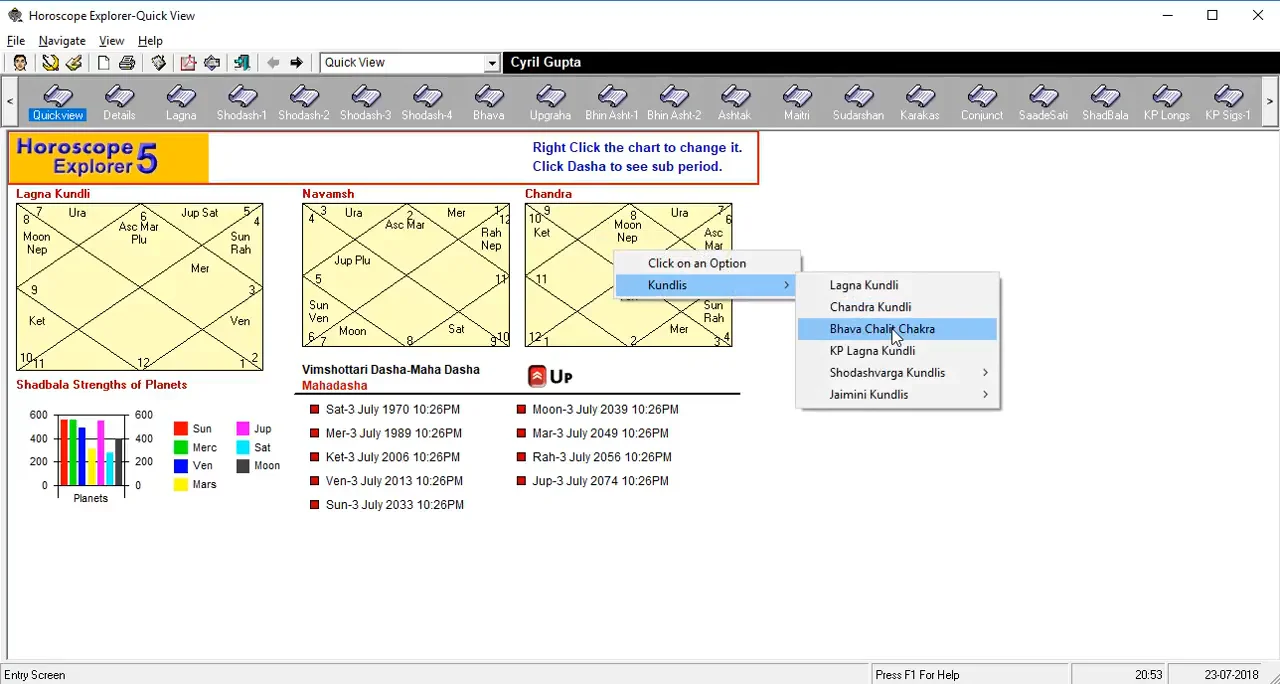
Astro Visual Software's Shop
In Stock
9984 Products Left$1500
$1125
25% OFF
Bingo Caller Pro Cracked: What You Need to Know**
Bingo Caller Pro is a popular software used by bingo hall operators to manage and automate their games. The software is designed to provide a reliable and efficient way to call out bingo numbers, track player progress, and manage game settings. However, like any other software, Bingo Caller Pro is not immune to cracking and piracy. In this article, we will explore the implications of Bingo Caller Pro being cracked, the risks associated with using cracked software, and what you need to know to protect yourself.
Cracking software is often done by individuals or groups who seek to circumvent the software’s licensing and protection mechanisms. They may use various techniques, such as reverse engineering, patching, or key generation, to bypass the software’s security measures.
Bingo Caller Pro Cracked: What You Need to Know**
Bingo Caller Pro is a popular software used by bingo hall operators to manage and automate their games. The software is designed to provide a reliable and efficient way to call out bingo numbers, track player progress, and manage game settings. However, like any other software, Bingo Caller Pro is not immune to cracking and piracy. In this article, we will explore the implications of Bingo Caller Pro being cracked, the risks associated with using cracked software, and what you need to know to protect yourself.
Cracking software is often done by individuals or groups who seek to circumvent the software’s licensing and protection mechanisms. They may use various techniques, such as reverse engineering, patching, or key generation, to bypass the software’s security measures.